In the world of fast competitive marketing, a lot of attention goes to the first company who develops a creative breakthrough and comes out with a cool new device first. New technology in the medical device market has resulted in several new products which include;...
Remote Engineers
Is the Windows Phone 8 Ready for the Enterprise?
Is the Windows Phone 8 Ready for the Enterprise? I suppose the short answer would be, 'compared to what?' I've been an Android user, an iPhone user, and now I'm using a Windows Phone 8 -- and I have my gripes about all of them. Of course the real problem is that I...
My Arsenal of Product Development Tools
There are so many tools that are available to help make the process of coding more efficient, less time consuming, and overall a better experience. There are a number of tools / configuration settings I utilize in my environment to help make my overall coding /...
Cyber Security in Medical Device Design
With the push by big technology players (Cisco, Google, Intel, etc.) towards connectivity in everyday devices, cyber security is becoming more and more crucial. This push is even seen in medical device design as the industry begins to move toward cloud-integrated and...
Ultrabooks Place in the Workplace
Ultraportable laptops and Ultrabooks have become the new machines to have. They are smaller, thinner, and lighter making them the preferred choice for most engineering and IT professionals over the older clunkier notebook workstations. Even before the push by Intel...
DIACAP Testing with Retina Network Scanner
Recently I took over DIACAP testing on a few machines. The task of starting DIACAP testing may seem overwhelming when presented with the number of tests and findings you will need to complete. Thankfully, there have been some automated tools released to help aid the...
Macs in a Corporate IT Environment
Macs running OS X have been around for quite some time, but only recently have they gained enough traction with our customers at SPK to be used as their day to day desktop environment. Historically, IT organizations have been reluctant to embrace this change. This...
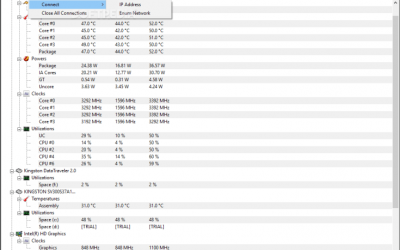
Upgrade to HWMonitor Pro and Make Your Computer’s Sensors Work For You!
Some time ago, I wrote an article about CPUID’s wonderful tool, HWMonitor. Today I want to follow up on that and give a few tips on how to make it more useful. Firstly, HWMonitor is a free tool, but CPUID publishes a Professional version of the product, predictably...
5 Minutes with Windows 8 and Office 2013
Dell Latitude ST This is the Dell Latitude ST, which can be had from the Dell Outlet store for about $300. It’s a 10-inch tablet slate running an Atom Z670 and 2GB of RAM – like a Netbook without a keyboard. Instead, it has an N-trig digitizer that supports both...
Distinguishing Between Virtual Teams and IT Outsourcing
One of the benefits of an IT outsourcing partnership is that it can offer companies the option of working with virtual teams who can help support different types of IT and business operations, regardless of the locations of the workers. Teams and team members who work...
From Out-of-Office to VPN in 15 Minutes
Traditionally, using a VPN (Virtual Private Network) to connect to a remote site has been a technical – and oftentimes troublesome – requirement. With the growing popularity of using “remote programmers”, I see requests for purchasing Cisco routers and Windows...
How to Backup an ESXi Server with GhettoVCB
VMWare is wonderful for getting full utilization of scarce resource. However, if you're on a limited budget, affording ESX clustered hosts for all needs is overkill. Sometimes a free ESXi server is enough. In the latter, we ran into challenges doing backups. ...