SentinelOne is an endpoint security tool. It offers cybersecurity protection for platforms including laptops, PC, phones, cloud servers and identity server protection. And it is the next generation in vulnerability endpoint protection platform (EPP).
SentinelOne is one of the best tools on the market to protect your IT infrastructure. Here’s why.
What is an EPP?
Gartner defines the Endpoint Protection Platform market as:
The facility to deploy agents or sensors to managed endpoints including PCs, servers and other devices.

What Are The Core Functionalities Of An EPP?
According to Gartner, the core functionalities of an Endpoint Protection Platform are:
- Prevention and protection against security threats including malware using file-based and file-less exploits
- The ability to apply control (allow/block) to software, scripts and processes
- The ability to detect and prevent threats using behavioral analysis of device activity, application and user data
- Facilities to investigate incidents further and/or obtain guidance for remediation when exploits evade protection controls
SentinelOne is named as a leader in 2021 Gartner Magic Quadrant for Endpoint Protection Platforms (EPP).
What Are The Benefits Of SentinelOne?
Protection from SentinelOne mean organizations can benefit from extensive enterprise security. It enables the discovery of vulnerabilities and enhanced IT operation protection. The agent platform allows users to detect threats and resolve system attacks.
SentinelOne is a cloud-based solution. Therefore, it empowers businesses (of all sizes) to manage the entire threat lifecycle.
Some of the best SentinelOne security features include:
1. Hunting Methodology
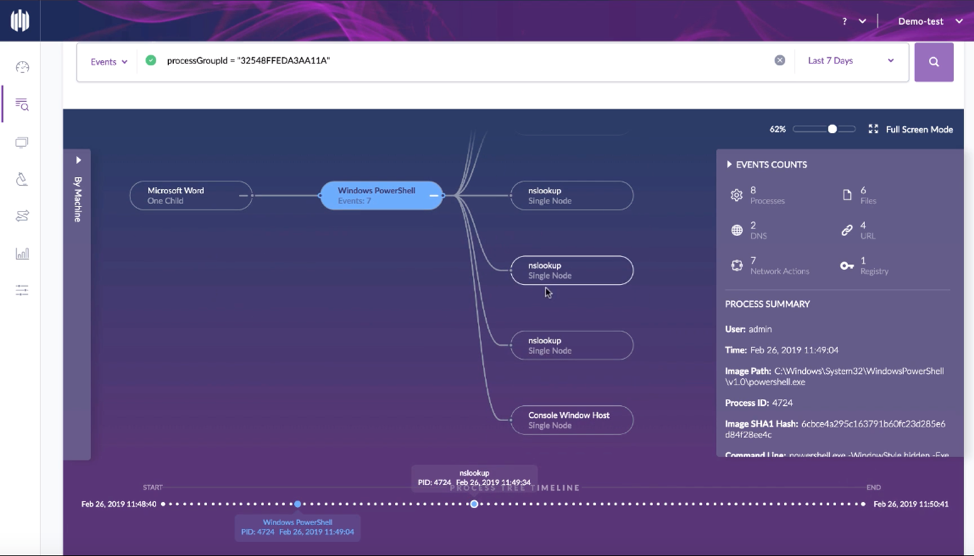
Proactive threat mitigation is what every organization should embed in the DNA of their IT ecosystems. Through employing a hunters approach threats can be caught before they have the opportunity to interfere with networks. SentinelOne delivers quick query times, and advanced actions when threat hunting. Additionally, the advanced SentinelOne features include pre-indexed forensic context. This enables organizations to understand the motive behind attacks, full-native remote shell, and more.
2. Real-Time Threat Detection With Artificial Intelligence
Real-time threat detection enables organizations to respond fast. It allows for effective mitigation of wider spread cost, reputation and operational damage. SentinelOne uses a patented behavioral AI feature to recognize malicious actions and patterns. Threat detection is applied to detect file-less, zero-day, and nation-grade attacks. Additionally, AI integration ensures threats are discovered in a timely manner which reduces the effects of ransomware and phishing attacks.
3. AI-Assisted Prevention Model
SentinelOne integrates Static AI on endpoints to prevent real-time attacks. This AI integration ensures threats are dealt with promptly. Before they can affect your network. By integrating with static artificial intelligence (AI) the SentinelOne prevention model is more effective than the historic anti-virus. It drastically reduces the number of false positives allowing you to focus on real-risk threats.
Furthermore, the artificial intelligence (AI)-based solution performs recurring scans to detect various threats including malware, trojans, worms and more.
4. Response Features
SentinelOne uses ActiveEDR to respond to network threat issues. ActiveEDR integrates behavioral AI. It is capable of both reversing and removing malicious activities. Organizations can automate the response process to ensure it occurs in real-time. Therefore, this AI response ensures devices connected to enterprise networks can individually respond to threats in real-time.
5. Whitelisting/blacklisting with SentinelOne
SentinelOne offers full visibility over the vulnerable applications on the devices the agent is installed on. It has the capability to do this due to its in-depth endpoint inspection. Also, it works in conjunction with data from the National Vulnerability Database(NVD) which is continuously updated. Subsequently, this means that newly discovered threats are prioritized, cataloged and added to a database daily. This means it is ready to detect and protect from threats. Conversely compared to waiting for a breach of new threats to be detected on an endpoint machine.
Through SentinelOne’s AI engine, an Exploit Shield is then used to detect and prevent any exploitation of the discovered vulnerabilities.
6. End User Experience
Legacy anti-virus users who have been through enough trial and error will have been exposed to plenty of anti-virus software. And, most will also have experienced the pain of slow systems due to anti-virus scanning. Organizational effectiveness should never be an “either-or” when it comes to protection or business as usual efficiency. That’s why SentinelOne does not slow down the endpoint on which it is installed. In fact, it is designed to have as little impact on the end user as possible. All whilst still providing effective protection both online and offline.
Can I Easily Integrate SentinelOne With Third Party Apps?
The application can also be deployed in an on-premise environment. Additionally, it can be integrated with various third-party applications.
Conclusion
SentinelOne protects your computer and data with anti-malware and anti-exploit protection. Named as a 2021 Gartner Magic Quadrant for Endpoint Protection Platforms (EPP) Leader, it’s no surprise why SPK and other engineering firms globally trust the use of this cybersecurity product with their customers. From hunting methodologies to great response features, AI modeling and more, SentinelOne really is the next generation of Endpoint Protection Platforms (EPP).
If you would like support to improve the threat mitigation on your networks or to deploy SentinelOne effectively, you can contact our expert cybersecurity team here for a no obligation discussion.






