Pretty much every day I do some system administration on one of our many Linux servers that we support as part of our managed IT services. It occurred to me that I use a bunch of utilities and tools within Linux to make my job easier and wanted to share my top 5 Unix commands you might not be using (but should be).
The key with Linux commands is making aliases for them, or if you want to do many things on a consistent basis, write a batch script and stick it in your cron. Shell scripting is a bit beyond the scope of this blog post, but it is a useful skill to learn as a Unix system administrator. Anyways, on to the Top 5!
1. Screen
Screen is utility that’s not normally included in every Linux distribution, but is often available to download either through a software repository for your distribution or pre-compiled packages. I highly recommend installing it on every Linux machine you manage. The utility allows you to open pseudo terminals within one session. So why do this instead of just opening multiple sessions? Well, the biggest reason is that if you lose your connection, you won’t lose your session. That’s right, if you’re working on a machine and your wireless network suddenly disconnects, you won’t lose any work you have in progress. Screen will maintain the session, but put the session into a mode called “detached”. So if you’re running a long rsync command, the command continues to execute even though you are not connected to the machine. Once you reconnect, you can “re-attach” to your screen session and you’re on your way! I’ll dedicate a future blog post to screen, but if you check out the main page for it, it should give you a good start to using this powerful command.
2. du
du stands for “disk usage” and it’s the best way to see how much space is being used in a directory. It’s a great way to see what users are taking up all the space on the machine’s disk, and be able to give them hard proof when you give them that stern talking to. I actually create an alias for du on every server I manage and name it “sdu”. The definition:
alias sdu=’du -h –max-depth=1′
What does this do? Well, the -h parameter tells du to output values in human readable format. I.E. M for megabytes, G for gigs, etc.. If you leave off the -h parameter, you get the results in bytes, so if you enjoy doing math, feel free to leave the -h parameter off. The ‘–max-depth=1’ parameter tells du to only report on the total size of every subdirectory in the current directory.
For example, if I want to see what each user’s directory is using in disk space in /home, I’d run this command:
sdu /home
This gives me a nice listing of every user’s directory with how much space they’re using.
3. ls
ls is a command everyone who works in the shell on a Linux server knows. It gives you a listing of files in your current working directory. I actually make aliases for this command and I thought I’d share a few of them.
alias lt=’ls -latr’ – This alias lists everything in the current directory but sorts them by reverse time, so the newest files are at the bottom. Great for when you’re in the /var/log directory and want to see what logs are being updated.
alias ll=’ls -la’ – This is a common command, often aliased to dir, but it basically shows EVERY file in a directory including dot files (i.e. .bashrc, .profile, etc..)
alias sls=’ls -sa’ – This will show everything in a directory but in column format. I love this command when I’m logged into a server on my iPhone.
4. find
find is extremely powerful. It can rapidly traverse large amounts of directories looking for specific files or directories and then actually perform commands on those found files/directories. One example usage for find is in a script I wrote to delete old log files off of a server after they reach a certain age. The find command I wrote:
find /var/log/web -name “access.log.*” -mtime +30 -exec rm -f {} \;
This find command will go through the /var/log/web directory and find that matches the access.log pattern and if it’s older than 30 days, it will remove it. One command to clean up hundreds of files and not lose data that you need. There are a lot of other uses for find, but that’s one of the most common.
5. top and free
Both top and free are commands you can use to monitor memory usage on your Linux machine. I have to include them together because top only shows a piece of the memory usage puzzle, and free fills in the rest of the puzzle. Top is used to monitor your system resources in real time. If you type top you’ll get a listing of vital system stats. It will show; the uptime of the machine, total processes in use, CPU usage, memory usage, and swap usage. It will then show a nice display of the top resource using processes, updated every few seconds. This is a great utility to find runaway processes that are eating all of your server’s CPU resources, as it will put the top process on the very top of the list. You can then see who’s running it and tell them to stop it.
Free on the other hand only focuses on memory (RAM) usage, but it breaks it down into the different types of memory that Linux allocates. Say you’ve got 32G of RAM in your Linux server. If you run top, it might say that you only have a paltry 1G available of free RAM. The key is the word FREE. That means this is RAM that has not been allocated by the kernel. If you run the free command like this:
free -m (the -m option says to output in megabytes, again, the less math you have to do, the better)
You’ll see something like this:
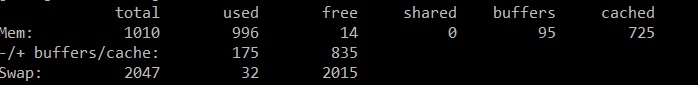
So this shows me that my machine has 1G of RAM, 996M is used, 14M is free, 95M is in buffers, and 725M is cached. Also, 32M has been used from swap. So what’s the difference between buffers and cache? Buffers is a temporary space in memory that is stored by a certain application. The data is not used by other applications. It’s just like if you send a burst of data over the network, your network card will buffer the data so you get constant speed and not drop packets because the card can’t keep up. Cache is memory that the kernel has allocated for use and if a new application needs memory, it will pull from cache memory. Both methods for storing memory are temporary and even the memory is not being used, it’s still reported as used by the top command. That’s why the free command needs to be used with top to see the entire puzzle of your memory usage.
I hope these useful Unix commands come in handy for you. If you’ve found some other cool commands you want to share, feel free to do so in the comments below!
Next Steps:
- Contact SPK and Associates to see how we can help your organization with our ALM, PLM, and Engineering Tools Support services.
- Read our White Papers & Case Studies for examples of how SPK leverages technology to advance engineering and business for our clients.
Bradley Tinder, Systems Integrator, SPK & Associates







