When involved in IT strategy consulting services, you need a way to keep track of passwords in a safe and accessible manner. There are a number of different options out there ranging from single machine managers to cloud-based services. The one I found to be a great mix of accessibility and security is the Pleasant Solutions Password Server.
While programs like KeePass are nice to have in smaller environments, having to rely on cloud services like Dropbox to give multiple users access to it is not the ideal situation. Anytime passwords are stored on a cloud interface, your data is not fully under your control. Pleasant Solutions allows you to setup your own Windows Server that will host the password management server and keep the database and in-memory passwords encrypted. From there you can decide if you want to keep server access restricted to the workplace or give a wider availability.
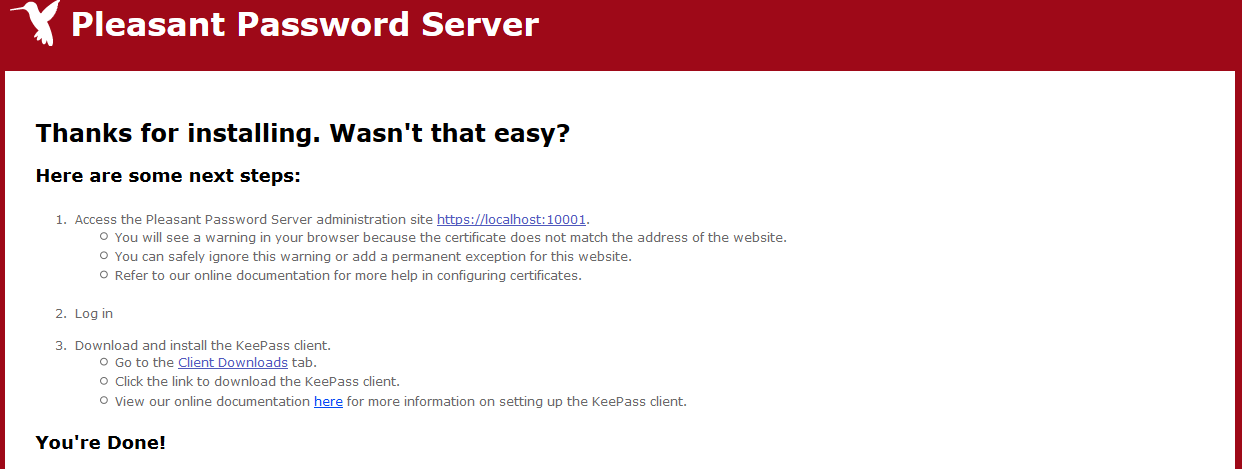
The installation of the server is nice and simple, you just need to run a downloaded exe on a machine running Windows XP or newer. The Server will automatically install a SQLite database for you to get the server started and load itself after the install ready to be configured.
The installation does start with a self-signed certificate that will be sufficient for general access. If you do want to support, the iOS app you will need to install a proper certificate. To configure server access a configuration program is installed on the host machine that can be used to edit the current port, certificate, database type, and save location of the application. This little tool makes it simple to find the path for your SQLite database so that it may be backed up as well as providing the encryption key that you will need to restore the database. At this point, the password server is ready to go internally. If you do want to add outside access, that just requires opening a port within your network configuration.
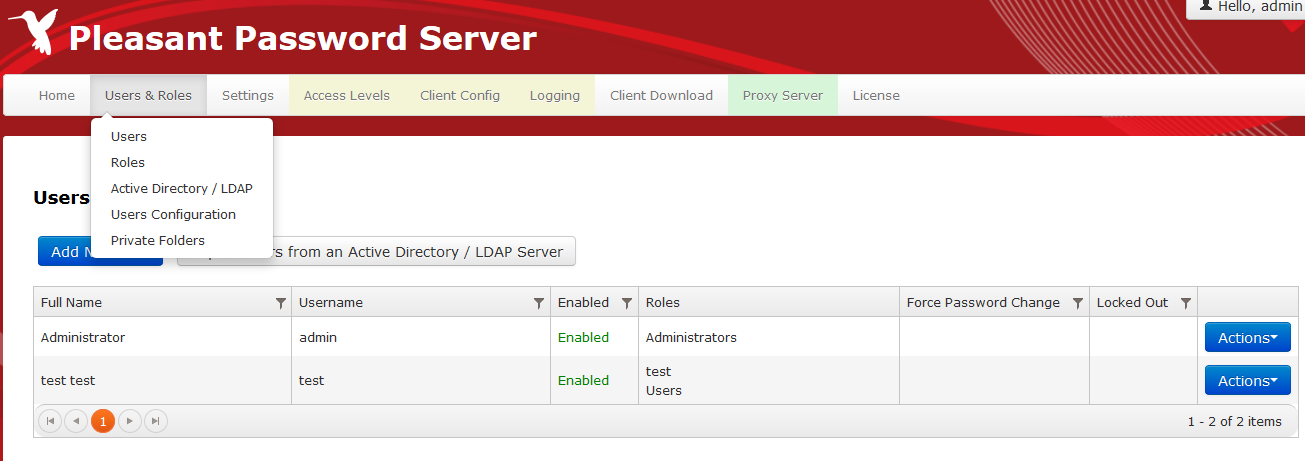
You are now ready to setup user accounts on the server. User configuration does need to be done through the web interface. If you happen to purchase the enterprise edition, you will have the ability to import users from Active Directory/LDAP Servers. Otherwise, you can add them by hand and have the ability to place the users in groups so that you can limit their access to passwords and categories. This lets you specify who can see or use the various features allowing you to restrict read or write access to individual items or folders.
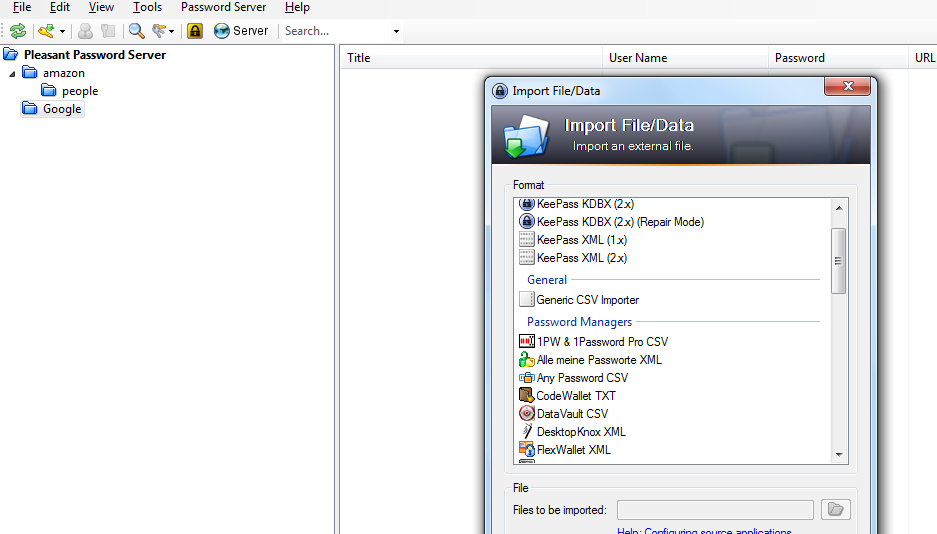
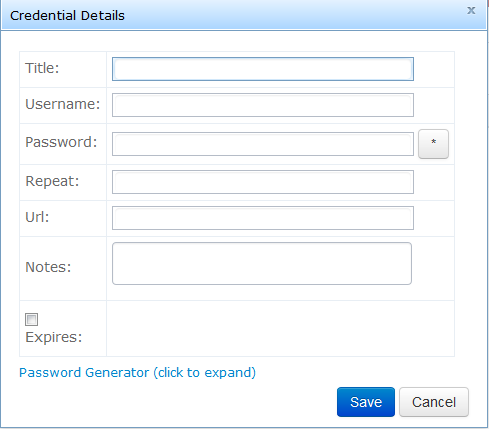
There are a few different ways that the system can be accessed to setup passwords. The easiest for a new password setup would be the web client that may be used to modify any settings within the system. This supports a wide variety of browsers and works on mobile browsers as well. The next option is through a custom Desktop KeePass Client that supports modifying passwords as well as importing passwords from a number of other password databases. While the device does have an iOS and Android app they are read only and do not support making any changes or adding passwords. The password fields do allow other information to be input as well as the user name and password allowing for helpful notes. The system also supports password revision history in case a password was mismanaged the previous can be found and restored.
I touched on the topic of backups and security earlier. The system is incredibly easy to backup. All that is required is to stop the Server’s service, go to the SQLite database file’s location, and make a backup of the file. Once that is complete, you have a backup of the database itself. All that is left is to back up the encryption key from the service configuration utility.
To restore your password database, you would again stop the service and then place the file back in the original location. Once you start the service up again, the system will be up and running right away. On the security end, the enterprise edition of the software provides logging functionality that will help you track which user account is being used to make changes to the system in the case of malicious activity. It logs access, changes, logins, etc making it quick and easy to track down whose account may have been compromised and get things running again.
On the pricing end, Pleasant Solutions has a onetime charge that supports a number of users. This can be upgraded to more users later and provides update support for 1 year. The lack of annual payments is another benefit of the software compared to other applications that have yearly fees and tend to be more expensive.
Next Steps:
- Contact SPK and Associates to see how we can help your organization with our ALM, PLM, and Engineering Tools Support services.
- Read our White Papers & Case Studies for examples of how SPK leverages technology to advance engineering and business for our clients.